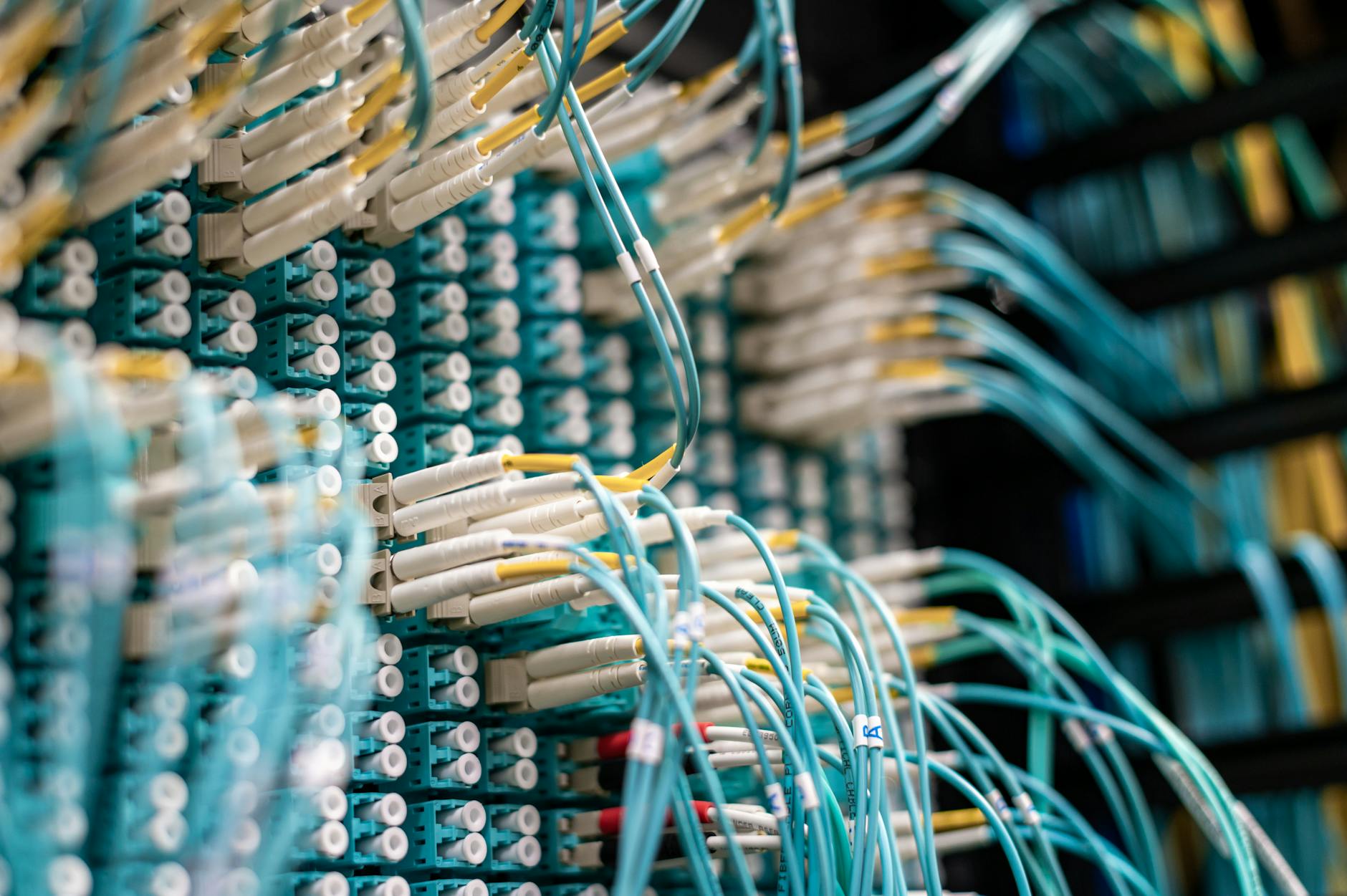
A new report from cybersecurity firm Ethiack reveals significant security vulnerabilities across the European telecommunications sector, involving more than 50,000 exposed digital assets.
Researchers analyzed 591 domains belonging to European telecoms to map the industry's attack surface. The study found that 37% of HTTPS connections use invalid or outdated SSL certificates, creating opportunities for man-in-the-middle attacks.
While a small number of large operators significantly inflate this figure, the report suggests the underlying issue of poor security hygiene persists across the sector. When excluding top outliers, the rate of invalid certificates sits closer to 17%.
Critical infrastructure vulnerabilities
The analysis also identified that 47% of web servers expose sensitive software and version information. This data allows cybercriminals to identify and exploit known vulnerabilities without additional reconnaissance.
Researchers identified 1,452 critical assets, including API endpoints, VPNs, and admin dashboards, showing concerning weaknesses. Webmail systems were particularly vulnerable, with 12% showing exposed configurations and 4% utilizing poor SSL practices.
"You can only defend if you know the map," said Ethiack CEO Jorge Monteiro. He noted that the increasing speed of exploitation, driven by rising CVE disclosures and AI, makes traditional periodic testing inadequate.
Ethiack's findings suggest that visibility gaps prevent security teams from protecting unknown assets. The report highlights that the 'time-to-exploit' for new vulnerabilities is approaching zero days, meaning attackers may strike before patches are even released.
To mitigate these risks, the report recommends implementing continuous Attack Surface Management (ASM) and AI-powered penetration testing. Such tools can identify and validate vulnerabilities at the speed of modern development cycles to prevent breaches before they occur.