Researchers have successfully developed a method to peer inside electronic components while they are actively running. This breakthrough allows experts to view the internal physical processes of hardware in real-time, moving beyond traditional diagnostic tools.
The team, currently focused on hardware security, intends to test whether this observational capability can extract encrypted data directly from chips. By watching the physical state of transistors as they process information, the researchers hope to bypass software-level security measures.
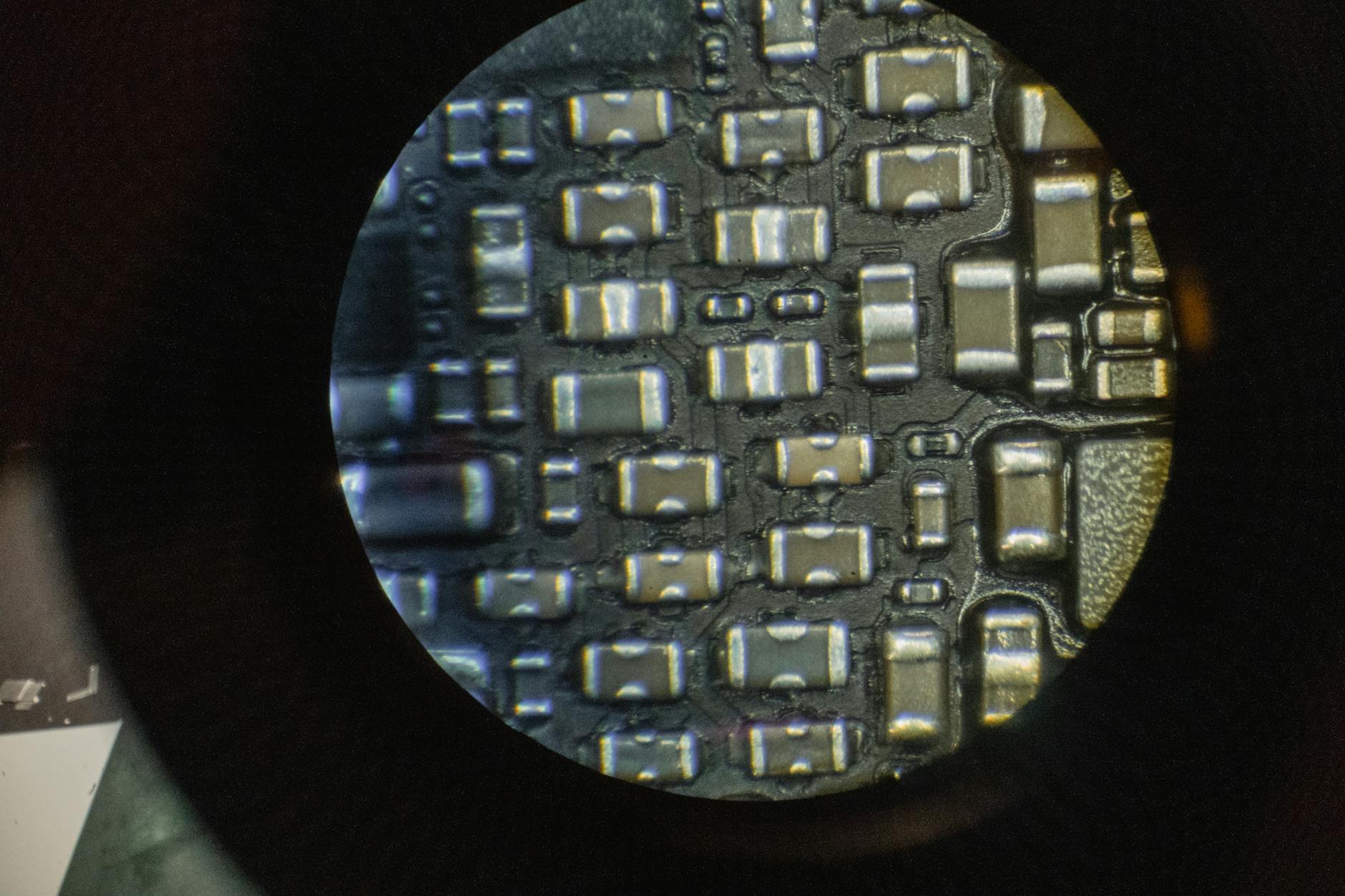
Visualizing Hardware Operations
Traditional methods for inspecting chips often require destructive processes or specialized equipment that only functions when the device is powered down. This new approach maintains the operational state of the hardware, providing a live feed of how data moves through the circuitry.
The researchers suggest that monitoring electromagnetic emissions or heat signatures during high-load operations could reveal patterns associated with encryption keys. If successful, this method could render existing hardware-based encryption protocols vulnerable to physical observation.
Security experts have long debated the strength of hardware-level encryption against sophisticated physical surveillance. This research provides a tangible look at how sensitive information might be compromised without ever touching the software layer.
While the technology is still in its experimental phase, the potential for monitoring hardware in real-time presents a new challenge for manufacturers. The team plans to publish further findings on their ability to isolate specific data streams from the complex noise of a modern processor. Their work indicates that the physical reality of hardware operation may soon become a primary target for security research.