Security researchers at Fenrisk have released MCPwned, a new Burp Suite extension designed to audit Model Context Protocol (MCP) servers for critical vulnerabilities.
The tool aims to address a rapidly expanding attack surface within the AI ecosystem. According to fenrisk.com, MCP servers are seeing significant growth, with approximately 100,000 hits for 'MCP' recorded on Shodan and multiple critical CVEs identified within the last month.
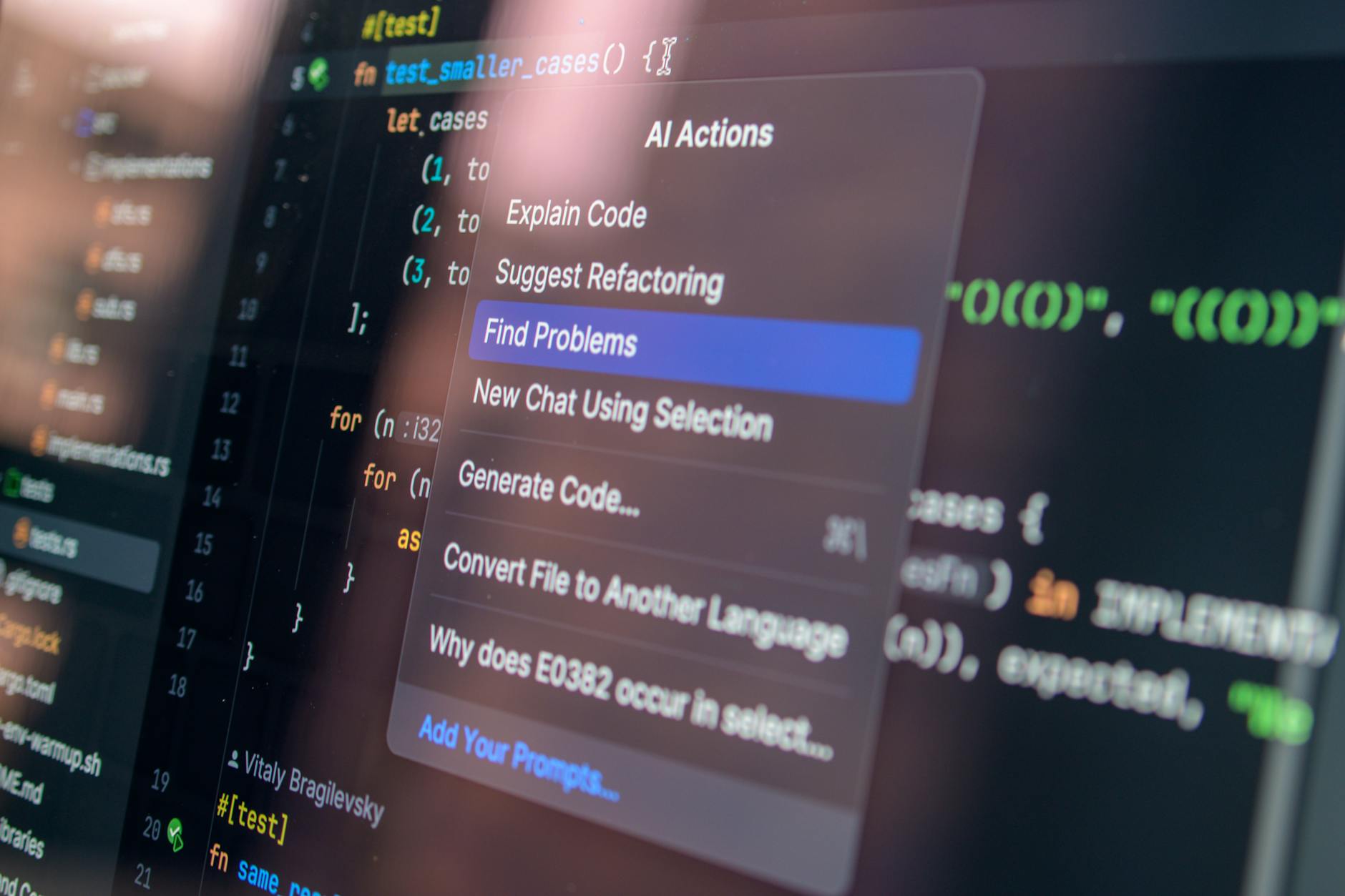
Developed by Raphaël Lacroix, the extension automates the detection of MCP traffic, enumerates server capabilities, and pre-fills payloads for testing tool arguments. The release comes as a response to the lack of dedicated security tooling for the protocol in industry-standard software like Burp Suite.
The security risks of AI connectivity
Originally released by Anthropic in late 2024, the Model Context Protocol allows Large Language Model (LLM) agents to interact with external systems, such as local files or remote APIs, in a model-agnostic way. The protocol has been rapidly adopted by major players including OpenAI, Nginx, and PortSwigger.
However, the speed of adoption has outpaced security implementation. The protocol allows clients to access 'capabilities' like tools and resources through local STDIO or remote HTTP transports.
Fenrisk reports that by default, the protocol contains no built-in authorization. This lack of native security measures, combined with the fact that MCP servers are not typically intended for human interaction, creates a dangerous oversight.
'This... can lead the developers to treat MCP as less exposed than the rest of their public facing attack surface,' the outlet reported. This mindset often results in insufficient input validation or a total lack of proper authorization.
In a demonstration of these risks, the researchers showcased a sample MCP server using 'FastMCP' that was intentionally vulnerable to command injection. By exploiting a tool designed to ping a network address, attackers could execute arbitrary commands on the host machine via the 'shell=True' parameter.
As the ecosystem expands, the researchers suggest that security professionals must prepare for a new class of AI-driven exploits. 'MCP servers are here to stay, so let's ready our tool belts,' the blog post stated.