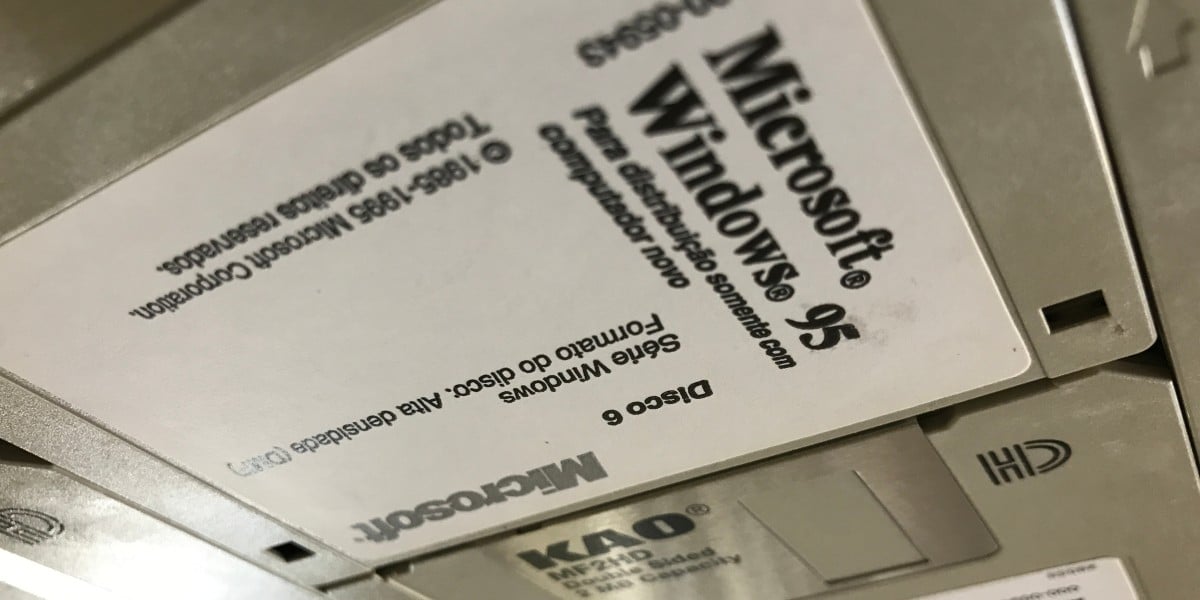
Microsoft veteran Raymond Chen recently revealed a hidden mechanism within Windows 95 that repaired system files corrupted by third-party installers.
This archival technical detail explains how the operating system managed to recover from aggressive setup programs that overwrote critical components.
The explanation highlights a unique approach to maintaining system integrity during an era of less restrictive distribution protocols.
Chen documented this process to shed light on compatibility strategies still relevant to modern computing history.
The issue originated during the transition from 16-bit Windows where many system components were legally redistributable by application vendors.
Installers were expected to compare version numbers before copying files ensuring they only replaced older components with newer ones.
This protocol relied on the assumption that all developers respected the backward compatibility guarantees provided by the operating system.
Consequently the architecture allowed significant flexibility that often led to unintended system instability.
In practice many setup programs ignored the versioning rules entirely to avoid dependency conflicts on the target machine.
It was not uncommon for these utilities to replace Windows 95 system files with older Windows 3.1 counterparts during the installation process.
Chen noted that this behavior frequently caused significant disasters for the rest of the system stability.
Users often faced crashes or boot failures after installing standard software packages from that period.
Microsoft could not simply block these file operations because doing so risked breaking the installer itself.
The operating system depended on backward compatibility meaning newer versions had to work even with older programs.
Blocking writes to system directories would have prevented legitimate installation attempts from completing successfully.
Therefore the company chose to allow the writes and handle the damage afterward instead.
Some installers declared the installation a failure when they could not overwrite the protected files.
Others displayed error messages to the user and asked for manual intervention regarding the conflict.
Even more extreme measures included rebooting the system to run a batch file that bypassed the file locks.
Chen reported that users rarely knew how to respond to these unusual requests from setup utilities.
Microsoft implemented a solution involving a hidden directory located at c:\windows\sysbckup.
This folder stored copies of commonly overwritten files to serve as a recovery reference point for the operating system.
The setup process relied on this backup location to restore correct versions after the installation completed.
This approach allowed the system to tolerate the initial corruption during the active setup phase.
After the installation finished Windows quietly checked file version numbers on the disk against the backup copies.
Higher version numbers were copied into the hidden directory or the backup file replaced the lower version number.
Essentially the operating system waited for each installer to finish and then went back to fix its work.
This automated repair process minimized the need for manual user intervention during troubleshooting.
This belt-and-braces approach depended on the operating system being aware of a setup program rummaging through its internals.
Today users should worry less about outside installers and more about changes Microsoft itself introduces to Windows.
The modern ecosystem has shifted focus from third-party corruption to system updates managed by the vendor.
Dependency management is now more complex but handled through different architectural mechanisms.