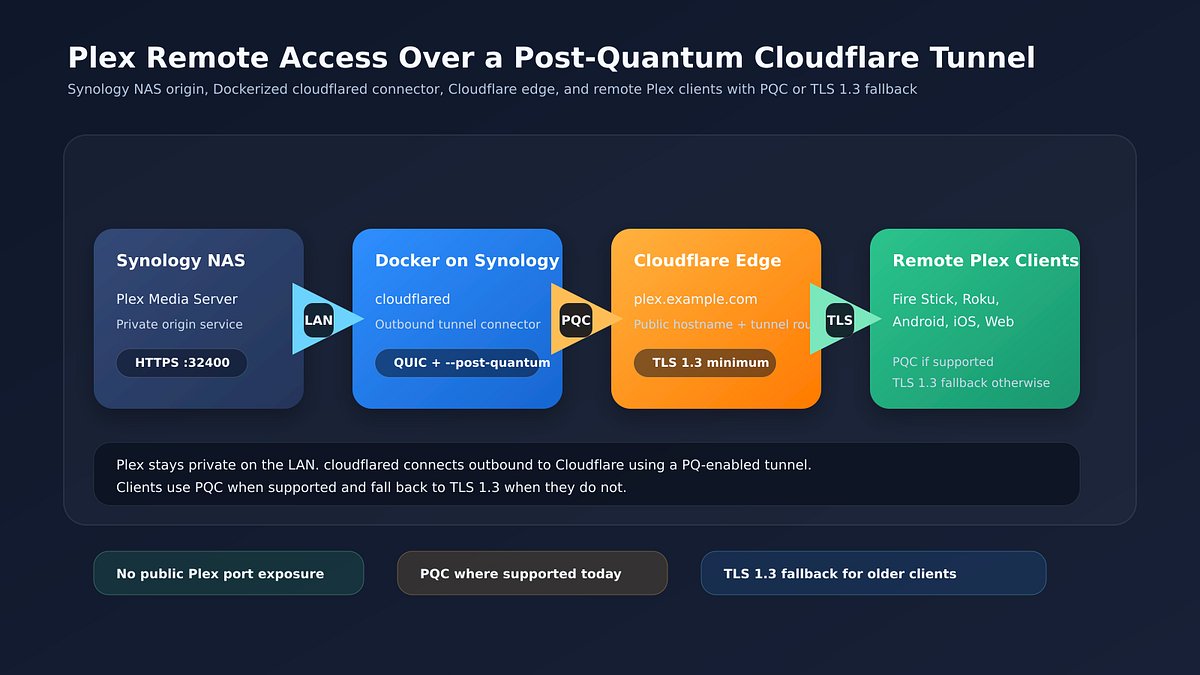
Security researcher Curtis Brazzell has outlined a new method for Synology NAS users to secure remote access to their Plex Media Servers by implementing post-quantum cryptography (PQC) tunnels. This configuration replaces traditional public port forwarding with a more resilient architecture designed to withstand the threats posed by future quantum computing.
Brazzell’s approach addresses two primary security concerns: the risks associated with exposing Plex ports directly to the internet and the need for encryption capable of resisting future decryption attempts by quantum computers. By utilizing a Docker-based setup on Synology hardware, users can route traffic through a secure tunnel that enforces advanced encryption standards.
Implementing advanced encryption standards
The configuration leverages a tunnel that mandates PQC between the user’s origin server and the network edge, while providing a fallback to TLS 1.3 for clients that lack quantum-resistant capabilities. This hybrid model ensures compatibility with existing devices while upgrading the underlying security transport layer for modern clients.
Brazzell initially utilized Cloudflare’s tunnel infrastructure to facilitate the connection. However, he subsequently refined the process to improve data privacy. "I ended up deciding to cut Cloudflare out of the middle by replacing cloudflared with a Synology-hosted reverse proxy," Brazzell noted in an update to his findings. By moving to a self-hosted reverse proxy, he ensured that traffic remains within his own infrastructure, preventing third-party intermediaries from monitoring the encrypted Plex data stream.
This method allows users to maintain external access to their media libraries without opening persistent ports on their home routers. The transition to PQC-ready infrastructure reflects a growing trend among security-conscious home server administrators who are looking to 'future-proof' their data in transit against long-term decryption risks.
For those managing personal media servers, the shift represents a significant move toward hardened network hygiene. While the prospect of quantum-based decryption remains a future concern, the industry-wide shift toward post-quantum standards suggests that early adoption of these protocols is becoming a standard practice for protecting sensitive private traffic.