The open-source AI application development platform Flowise has been hit by a severe remote code execution (RCE) vulnerability, tracked as CVE-2025-59528. Security researchers have confirmed that the flaw is already being actively exploited in the wild.
Vulnerability Overview and Threat Analysis
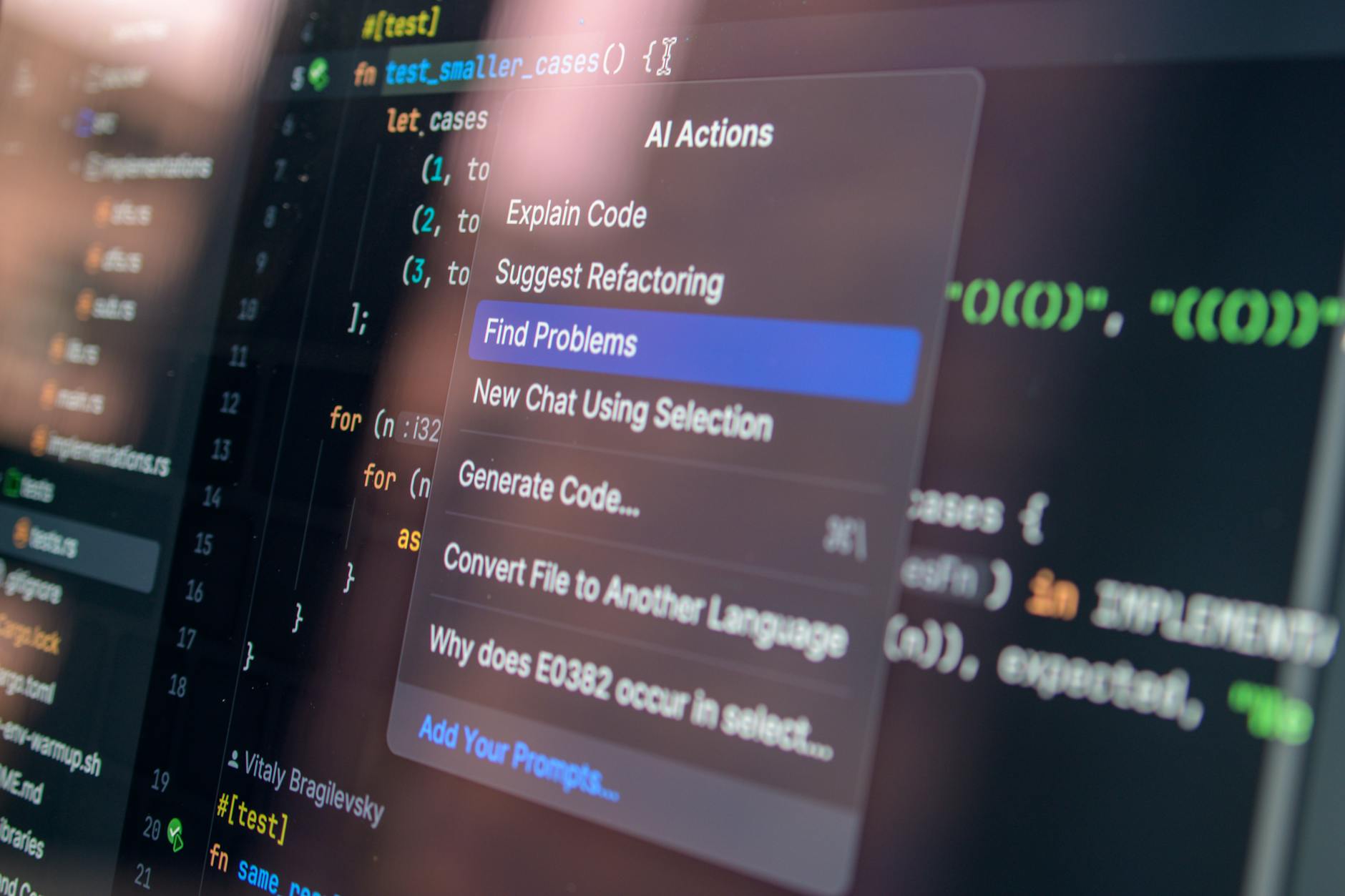
The vulnerability resides within Flowise’s CustomMCP node. Because the system fails to properly sanitize user-configured 'mcpServerConfig' inputs, attackers can inject and execute malicious JavaScript code. Disclosed last September, the vulnerability carries a maximum CVSS score of 10.0, meaning that a successful exploit allows attackers to execute arbitrary commands and gain direct access to the underlying file system.
Caitlin Condon, a researcher at vulnerability intelligence firm VulnCheck, issued a warning on LinkedIn. She noted that VulnCheck’s canary network detected the first exploitation attempts targeting this flaw. While the current activity appears limited and originates from a single Starlink IP address, the risk remains significant.
Flowise is a low-code platform primarily used for building AI agents and workflows powered by large language models. Thanks to its drag-and-drop interface, it is widely used for developing AI prototypes, chatbots, and automation systems. Estimates suggest that between 12,000 and 15,000 Flowise instances are currently exposed to the public internet. While the exact number of vulnerable servers is unclear, the potential attack surface is massive.
Condon pointed out that in addition to CVE-2025-59528, Flowise has previously been affected by other vulnerabilities, such as CVE-2025-8943 and CVE-2025-26319, both of which also have records of exploitation in the wild.
Flowise developers addressed this security flaw in version 3.0.6. Officials strongly advise all users to upgrade to the latest version, 3.1.1, immediately. For organizations that do not require external access, experts recommend taking these instances offline to completely eliminate the potential attack vector.